Human Authenticity Infrastructure · Human Verified Actions
Replace static credentials with biometric-backed, human-verified approvals.
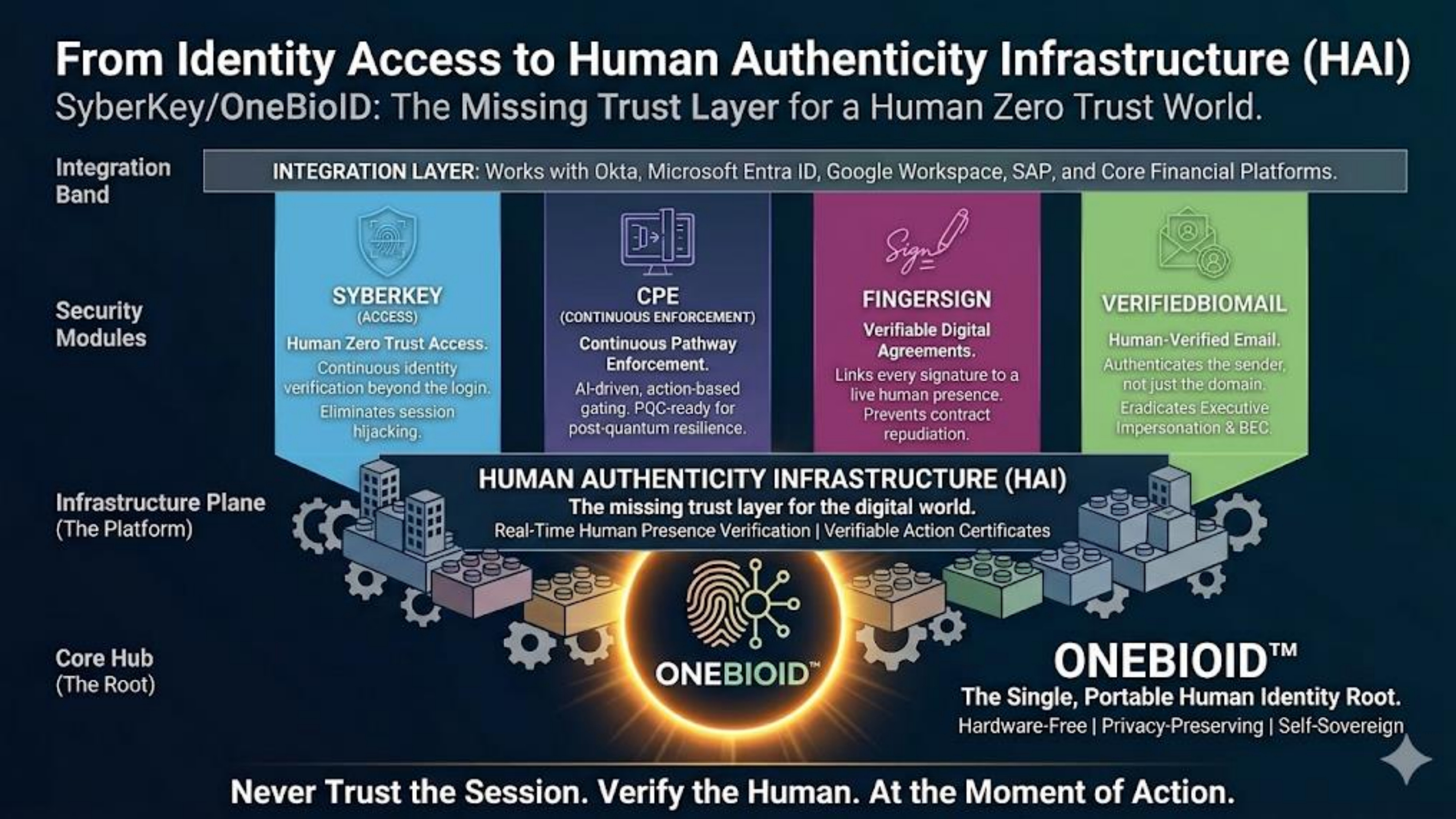
SyberKey / OneBioID — hardware-free remote biometrics and a modern identity architecture that shrinks attack surface by removing reusable secrets.
Video: Platform overview
Video: SyberKey CPE presentation
Static credentials and weak identity workflows are a structural risk.
Passwords, OTPs, shared secrets, and bolt-on MFA create phishing surfaces, credential replay, and operational drag. Legacy biometrics often depend on dedicated hardware or repeated scans.
- Identity is the perimeter — most breaches still involve credential misuse, MFA fatigue, or session abuse.
- Digital systems often verify credentials, not human presence at the moment of a sensitive action.
- AI-generated impersonation and deepfakes increase pressure to prove who is acting — not only which device holds a secret.
Human-verified actions on the device people already carry.
Push-based approvals, secured remote biometric verification, and cryptographic path enforcement align identity decisions with policy — without transmitting static templates or reusable secrets.
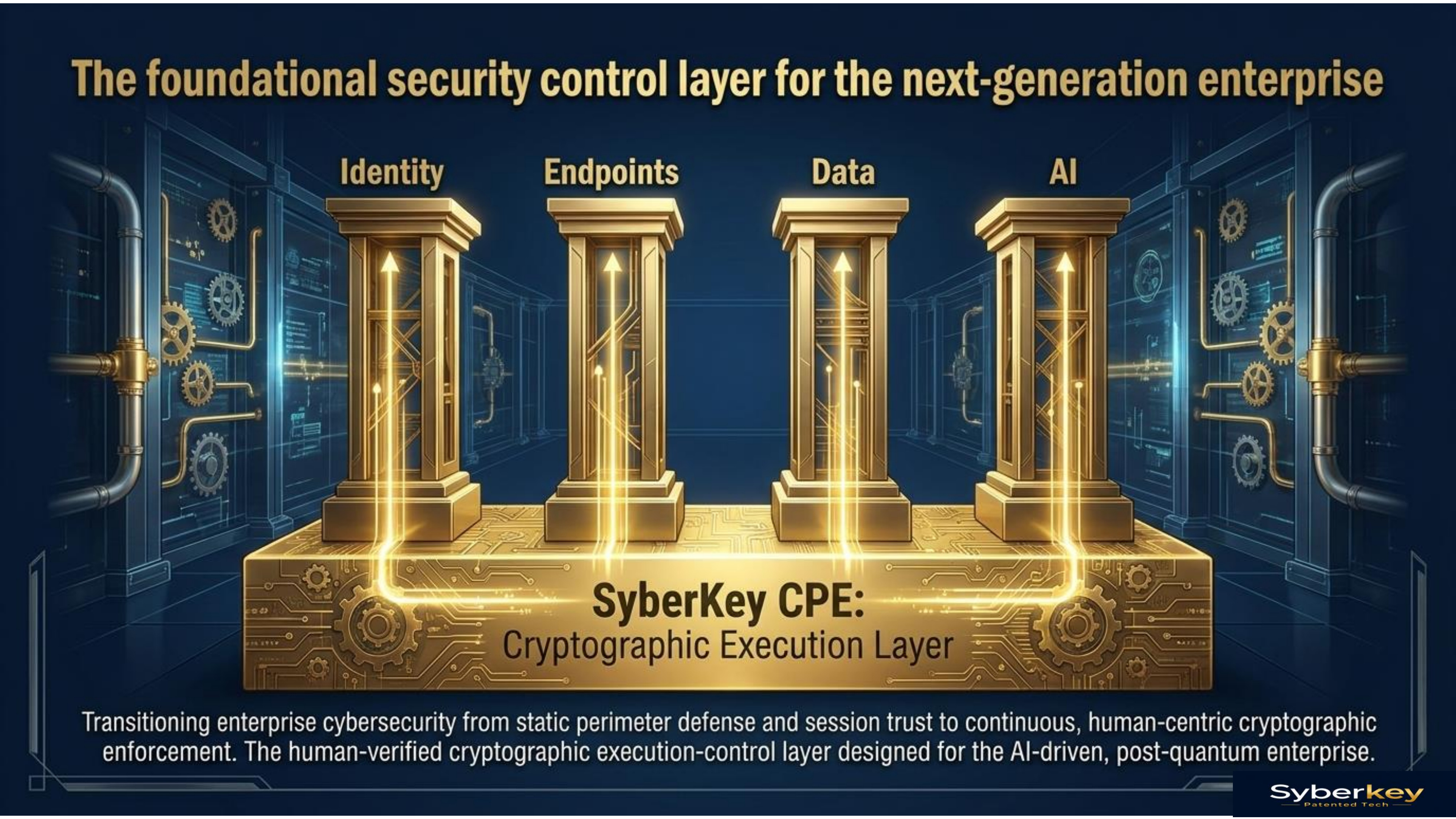
Where traditional stacks rely on session trust after a single MFA event, SyberKey emphasizes continuous enforcement for high-impact paths — reducing blast radius when sessions or tokens are abused. Framework concepts such as Human-Rooted Identity Assurance (HRIA) and a continuous biometric identity fabric complement this model in enterprise deployments.
How we secure trustCredential security → human authenticity
The market has spent decades hardening credentials. SyberKey is built for a model where trust is anchored in verified human identity and presence — not static secrets.
- Identity = credentials & devices
- Secure login, then session trust
- Vaulted secrets & backend-only assurance
- Identity = human verification
- Secure every sensitive action — continuous enforcement
- No long-lived static secrets; independent assurance layer
Digital systems increasingly need all three — not only “who logged in.”
Built for enterprise identity workflows
Four core capabilities you can deploy together or as modules.
Request → approve → verify → decide
A consistent pattern across channels and applications.
Users enroll once with a portable, hardware-free One Bio ID experience. When a sensitive action requires it, execution can pause until a presence assertion completes — producing a non-repudiable approval aligned to policy.
Request
Application or policy engine initiates a secure approval request.
Push
User receives a contextual prompt on a trusted device.
Verify
Remote biometric verification without transmitting static templates.
Decide
Cryptographic decision and audit trail align with policy.
Where teams deploy SyberKey
Industry playbooks with outcomes — not generic buzzwords.
Designed for quantum-aware, enterprise-grade posture
SyberKey emphasizes cryptographic-layer control, responsible AI positioning, and PQC readiness — articulated in a way security teams can evaluate.
Read architecture overview- Credential elimination architecture (no static secrets as root of trust)
- Action-bound approvals & policy-aligned decisions
- Audit-friendly flows & PQC-aware roadmap alignment
Evidence for your evaluation
Official PDFs — formatted for web discovery.
See SyberKey in your environment
Talk with our team about pilots, integration requirements, and security review materials.
Request demo